- Researchers from KU Leuven university in Belgium demonstrated that hackers can secretly clone the key fob of a Tesla Model S and steal the car within seconds – and with only $600 worth of simple computing and radio equipment, WIRED reports.
- The researchers brought their findings to Tesla – which rewarded them for exposing the security flaw – and Tesla responded by adding a software update with two factor authentication using a PIN code, and it offered updated key fobs to customers with additional security.
- However, if Model S drivers haven’t updated their software and don’t have a new key fob, their cars are still theoretically vulnerable to this type of theft.
A savvy car thief could drive off with a Tesla Model S by using just a few, relatively inexpensive pieces of computing hardware and some radios – at least, the thief could have until recently, when Tesla fixed an overlooked vulnerability in its cars’ security systems.
A group of researchers from KU Leuven university in Belgium demonstrated that Tesla Model S key fobs can be cloned, and the cloned signal can then be used to unlock the vehicle and start the engine – all without the owner realizing, WIRED reports.
The researchers brought their findings to Tesla last summer, and the company rewarded them with $10,000 for exposing the security flaw. In response, Tesla released a software update in August that enabled two-factor authentication with a PIN code from within the vehicle. It also developed and released updated, encrypted key fobs with additional security. If customers updated their software and received a new key fob, they should be safe from these types of attacks, but customers who didn’t install the update or who don’t own the new fobs are still theoretically vulnerable.
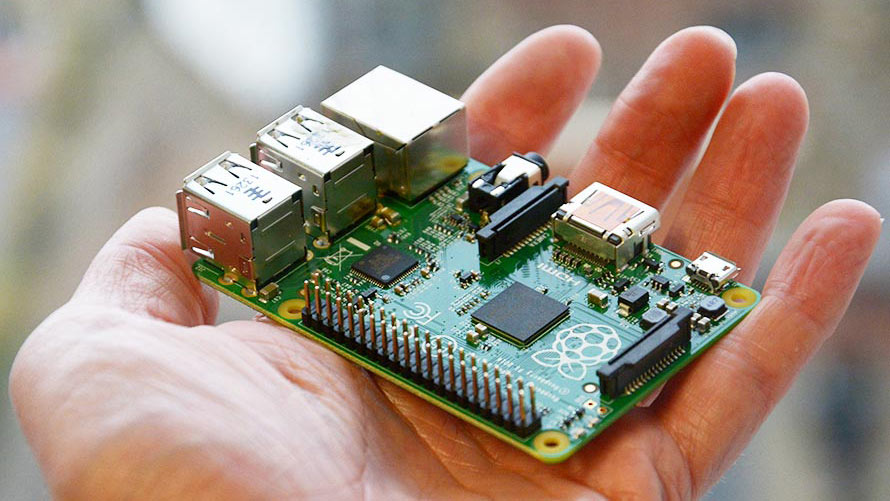
The amount of work that goes into the hack is surprisingly minimal, and not much equipment is needed. All of the necessary hardware costs less than $600, and the Model S can be hacked within seconds without the owner realizing it. The researchers built their device with a Raspberry Pi computer, a Yard Stick One radio, a Proxima radio, an external hard drive, and batteries.
A clever, and worrisome, hack
The researchers began by building a database of all the possible digital entry keys that could be used to open a Model S. The result was six terrabytes worth of potential keys - which are stored on the device's hard drive.
After that, it's simply a matter of following these 4 steps:
1. The hacker needs to copy the locking system signal that is constantly emitting from the Model S itself.
2. Next, the hacker has to take the radio within about three feet of the victim's key fob, and using the signal that was copied from the car's locking system, they trick the fob to emit two response codes that would normally be sent to the vehicle.
3. The hacker then need only run the signals through the database of possible keys stored on the hard drive, and the car's digital key will be located within seconds.
4. Then the hacker can return to the car, open the door, and drive away without the owner having any idea. Once the digital key is discovered, the hackers could clone the key fob and make one of their own - meaning they could enter and start the vehicle whenever they please.
Here's a video of the hack being demonstrated:
In a statement to WIRED, Tesla said that it had needed time to verify the authenticity of the flaw, identify a solution, and then roll it out via a software update and through the production line of new cars. Tesla's solution should technically stop this type of attack - the two-factor authentication and encrypted key fobs that aren't vulnerable to hacking are most likely efficient countermeasures. In addition, Tesla added the ability to disable the "passive entry" feature, requiring the driver to physically press a button on the key fob to unlock the car.
Although the problem appears to be fixed, and there aren't any reports of this method being used to steal a Model S, it's an interesting development in cybersecurity. As cars become more high-tech, new threats arise as well that need to be addressed.