- A slew of data breaches, exploits, and backdoor hacks have compromised the private data of hundreds of millions of users in 2019 so far.
- Growing trends include supply-chain attacks, where hackers break into a company’s software that’s in turn distributed to clients, and ransomware, which can take your computer virtually hostage until you pay a ransom.
- Most high-profile hacks this year seem motivated by money, but a few have been traced to governments across the globe aiming to surveil individuals.
- Visit Business Insider’s homepage for more stories.
Nearly nine months in, 2019 has been a banner year for cybersecurity crises, with hackers targeting government agencies and private corporations alike.
Data breaches are not a new phenomenon, and federal agencies have acknowledged the constant threat of exploits. But 2019 has seen unprecedented attacks, including on systems that were previously seen as impenetrable, like Apple’s iOS.
Most high-profile hacks this year were done with clear monetary aims, rather than carried out by spies or hacktivists. On a few occasions, however, hacks have been traced to governments across the globe attempting to surveil individuals.
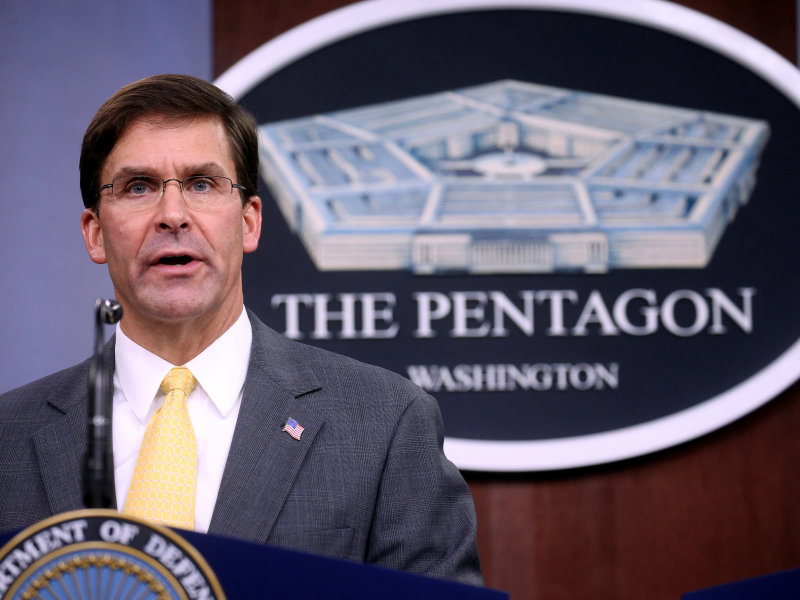
Last week, the US Department of Defense released a highly-anticipated new draft of cybersecurity standards, which tightens the norms that government contractors need to abide by for fending off hacks. The DOD is expected to issue its final framework for cybersecurity standards in January, according to FedScoop.
Here's a look at the biggest hacks - representing the most users affected or the most impressive feats of hacking - from 2019 so far.
WhatsApp was hacked and spyware was installed on users’ phones

In May, Hackers were able to install surveillance technology on the phones of WhatsApp users who answered their phone calls through the app, the Financial Times first reported.
It's unclear how many users fell victim to the attack. WhatsApp has over 1.5 billion users worldwide.
The FT reported that the spyware was designed by Israel's NSO group, and WhatsApp said in a statement that the hack bore the hallmarks of a private organization accustomed to working with government agencies. The Israeli firm denied any involvement.
An unprecedented iPhone hack targeted Uighur Muslims in China

For two years leading up to last month, "hacked websites" were used to attack iPhones, with every iPhone potentially vulnerable, according to Forbes.
The sophisticated hacks were discovered by cybersecurity researchers with Google's Project Zero, who announced last month that iPhone users who visited certain malicious websites could be vulnerable to surveillance across the phone's entire software, including passwords, messages, and location data.
The attack bore the signs of a state-backed effort, and was likely an attempt by the Chinese government to monitor Uighur Muslims, TechCrunch reported.
Apple downplayed the scope of the attack in the days following Google's announcement, stating that the problem was patched within 10 days of the discovery and that the malicious websites comprised "a few dozen" sites specifically targeting Uighur users.
Hackers stole US Customs and Border Protection data, including travelers’ faces and license plates

In June, hackers breached a database of images kept by US Customs and Border Protection, including photos of travelers' faces and license plates, the agency announced at the time.
The breach could have affected data of up to 100,000 travelers, according to the Washington Post. CBP stated that the images were obtained through a subcontractor's network but declined to name the subcontractor.
But in the title of the Word Document containing CBP's announcement of the breach, the agency named a subcontractor that offers license plate reading technology - Perceptics - suggesting that the company may have been involved in the breach. Business Insider has reached out to Perceptics for comment.
A federal defense contractor was hit by Emotet malware
Just this week, a government tech contractor based in Virginia was hacked and several of its systems were put up for sale on the dark web, cybersecurity watchdog Brian Krebs reported.
The extent of the damage from the breach wasn't immediately clear. The contractor had ties to the US Department of Transportation, the National Institutes of Health, and the US Department of Homeland Security.
The contractor, Miracle Systems, was hit by a malware strain known as Emotet that is typically distributed through email attachments. Miracle Systems CEO Sandesh Sarda told Krebs that the compromised systems were part of the firm's test environment and "no longer valid," but the Secret Service was investigating the hacks as of Monday.
A Quest Diagnostics breach exposed 11.9 million patients’ medical and financial data

Quest Diagnostics, a clinical laboratory, announced in June that an unauthorized user had accessed data on nearly 11.9 million patients, including credit card information and social security numbers.
The company did not immediately release details of how the breach occurred, but said that the unauthorized user had access to the information for months between Aug. 1, 2018 and March 30, 2019, Reuters reported.
The company blamed for the breach was American Medical Collection Agency, a debt collector that handled the data. AMCA lost its four largest clients including Quest following the breach and filed for Chapter 11 protection, aiming to liquidate, according to Bloomberg.
Hackers broke into Microsoft’s Visual Studio and seeded backdoors into at least three video games

Microsoft found in April that hackers hijacked its development tool Visual Studio, seeding backdoors into three video game companies that use the tool. As many as 92,000 computers were running malicious versions of the affected video games, according to WIRED.
WIRED reports that the group responsible is likely a mysterious Chinese hacker collective known as Barium, which has been on a hacking spree for years.
The attack is an example of a supply chain hack, where hackers seed malicious code into a company's software that is in turn distributed to clients. In this case, the supply chain hack was especially difficult to detect because the video game companies digitally signed their software before distributing them, marking them as legitimate even though they contained malware.
Ransomware attacks continued to sweep local governments throughout the U.S.

Continuing a trend from years past, hackers used ransomware to extort state and local governments across the nation for money throughout 2019.
Targets this year included the city of Baltimore, a Georgia court agency, a group of cities in Florida, and several local agencies in Texas.
While the Florida cities agreed to pay over $1 million in ransom, the other municipalities refused to pay hackers, instead shelling out millions of dollars to rebuild their IT infrastructure from scratch and protect against future attacks.
Fortnite warned 250 million players of a hack after some were hit with ransomware

Fortnite users were warned of a hack in August after some players were hit with ransomware that encrypted files on their computer and demanded payment for them to be unlocked.
The online video game warned its massive user base against downloading a supposed aimbot cheat tool, which claimed to give players an edge over competitors but actually loaded their computers with ransomware, according to Forbes.
To avoid the hack, users were given simple instructions: Don't download third-party software to cheat.
Hackers installed backdoors on thousands of ASUS computers using its own software

In an attack that began last year but wasn't discovered until 2019, hackers installed a malicious backdoor in thousands of computers made by Taiwan-based hardware giant ASUS.
The operation, first reported by Motherboard, placed malicious files in an ASUS software update, which the company unwittingly distributed to users through its Live Update Utility feature.
The group responsible for the hack is likely the China-based Barium, according to WIRED. Barium is also believed to be behind the supply-chain hack of Microsoft's Visual Studio this year.
Manufacturing firms across the globe were struck by LockerGoga ransomware attacks

Since the start of the year, at least five manufacturing firms have fallen victim to ransomware known as LockerGoga.
Like other aggressive forms of ransomware, LockerGoga can shut down computers and lock out users until they pay hackers a ransom. The malware can also shut down physical equipment, temporarily crippling manufacturing companies.
According to WIRED, firms hacked by LockerGoga found that their files had been encrypted within minutes. The only accessible file was a "ReadMe" file that said, "Greetings! There was a significant flaw in the security system of your company. You should be thankful the flaw was exploited by serious people and not by some rookies. They would have damaged all your data by mistake or for fun."
Tens of millions of peoples’ banking information was stolen in a Capital One data breach

In one of the largest hacks of a financial institution in history, Capital One announced in July that it had suffered a data breach, impacting tens of millions of credit card applicants.
Users' banking information, including transaction history, balances, credit scores, and addresses, were stolen. Some peoples' social security numbers were taken, but credit card information was not compromised, Capital One said at the time.
Paige Thompson, a software engineer who previously worked for Amazon, was arrested and charged with computer fraud and abuse in connection with the hack. She could face up to five years in prison and a $250,000 fine if convicted.

